 “If you know the enemy and know yourself, you need not fear the result of a hundred battles.
If you know yourself, but not the enemy, for every victory gained you will also suffer defeat.”
~ Sun Tsu ~
The Art of War
“If you know the enemy and know yourself, you need not fear the result of a hundred battles.
If you know yourself, but not the enemy, for every victory gained you will also suffer defeat.”
~ Sun Tsu ~
The Art of War
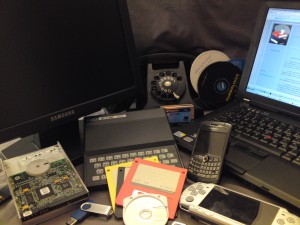
Apple Mac Operating System X versus Microsoft Windows Operating System
In a couple of days there will be an announcement that discloses twenty vulnerabilities for the Apple Mac Operating System X, OS X.
We have all seen the Apple commercials, right? They claim that their Apple computer is more secure than the PC? Do you believe them? If so, you are not alone, one of my family members recently bought an Apple. I asked him why, and the response was: it is more secure. Really, my heart nearly stopped, and I am only in my early 40’s.
(By the way, the commercials are very funny, and they are still on YouTube.) But are Apples more secure, and is that a reason to purchase an Apple?
All computer operating systems, whether Microsoft, Apple Mac, or Linux are vulnerable to attacks. Vulnerabilities are similar to an open window in your house. You may be able to put a lock on one of the windows, (no pun intended), but with an operating system, you will never be able to close and lock all of your windows. So you must practice safe habits while using your computer and surfing the Internet.
This is not an article to say that one computer is better than the other. This article is to help you, the consumer, make an informed decision. If someone says I really like the extra functionality, such as iLife, the multimedia tools that are included with Mac, then I get it. However, I most often find that like my family member, the purchaser is only interested in surfing the net and reading email; so why are they paying so much extra money for functionality that they are never going to use?
Now, let’s get to the heart of the issue, security. The twenty vulnerabilities that will be disclosed in the Apple Mac OS X are a lot of vulnerabilities for a company, which in my opinion, compared to Microsoft, does not take patch management seriously. The second Tuesday of every month, Microsoft releases security patches for their products; these Patch Tuesdays, assure clients that Microsoft is trying to address the publicly disclosed vulnerabilities.
There are articles that state that Mac is a safer, but not necessarily more secure product. What does that mean? This is a confusing point to most consumers, who are looking for a computer. In keeping with our house analogy, think of vulnerability as a prefabricated window which came from the factory with a lock that appears to work, but can easily be disengaged. Thus a thief can unknowingly come upon the faulty lock, and break into your home easily; or a workman may become aware of this lock, and thus target your house because he knows that you are vulnerable. In the computer world, what this means is that there can be a built in error or a weakness which creates an opportunity for your system to be breached. The argument is that Mac is breached less often; this may be true, but only because there are fewer people using Mac.
If you are the thief, who are you going to target? To date, more than 90% of personal computer users are working in a Windows environment. As we stated last week, most hackers are now working for financial gain. Thus, if you are looking to exploit a vulnerability, are you going to be bothered with less than 10% of the market? This does not mean that Apple users will never be exploited, because they have been, in the past. Obviously, with the attacks impacting such a small number of people, the press does not cover these incidents in the same manner.
So, when you go to make your next computer purchase, think about what you will be using your computer for? Are you interested in cool graphics, word processing, creating spread sheets, or surfing the net and staying connected? If you decide to buy an Apple because it meets your needs, then great; but please do not tell me it is because you think Apple is more secure – let’s stay connected.
http://www.macworld.com/article/140793/2009/05/macsecurity.html http://www.macworld.com/article/140873/2009/06/apple_java_security.html If you would like to comment on this story, please click on the accompany picture, which will take you a comment page. Thank you.