Smalltalk, it’s a Cleveland Thing
Yes, as a former Clevelander, I am playing with the word, Smalltalk. But did you know that one of the inventors of Smalltalk was from Cleveland, Ohio, and a woman?
First, what is Smalltalk? Simply put, Smalltalk is a programming language that was created as a method for humans to interact with computers, known as human-computer symbiosis. An example of human-computer symbiosis would be a person interacting with a keyboard on a computer to navigate the Internet.
Second, who is Adele Goldberg; Adele Goldberg was born in Cleveland, Ohio, and grew up in Chicago, Illinois, where she would attend the University of Chicago for her master’s and PhD in information science, completing her studies in 1973.
Goldberg would then head to Xerox Palo Alto Research Center PARC. And it would be at PARC that she, Alan Kay and Dan Ingalls, would develop Smalltalk, an object-oriented programming language that would give birth to one of the most important features in our interaction today with digital devices, known as the Graphical User Interface GUI.
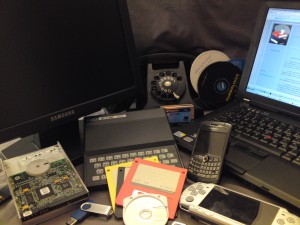
Both Mac OS and Windows would use Smalltalk and incorporate elements of the programming language such as, a mouse and pop-up menus. For many of us in the computer industry, prior to a GUI, we would interact with a green screen. The green screen consisted of a dark background with green characters and a person would have to have a considerable amount of computer knowledge in order to extract the necessary data from computer programs.
Smalltalk was originally conceived as a programming language to be taught to children. The name Smalltalk came from Alan Kay, who had a reaction against the Indo-Europeans where the systems had names like Zeus, and Thor, and never did anything. Alan thought that the innocuous label of Smalltalk would set expectations appropriately, and if anything did come of the programming language, that people would be pleasantly surprised. http://worrydream.com/EarlyHistoryOfSmalltalk/
And what a pleasant surprise Smalltalk has been. The object-oriented language would steer some of greatest digital achievements such as the language virtual machine, vm, just-in-time compilation, integrated development environment IDE, and software architectural pattern model-view-control MVC.
Smalltalk would also lead to another digital idea, Dynabook, in 1977, invented by Kay and Goldberg. The Dynabook was an idea where every individual would use a notebook computer to interact digitally with others; today we would call this a laptop.
And probably one of the greatest outcomes of Smalltalk would be the Macintosh. Steve Jobs and the direction of Apple would pivot completely once he saw Smalltalk and WIMP, windows, icons, menus and pointer.
In fact, when Steve Jobs wanted a demonstration of Smalltalk System, it was Goldberg who would refuse him. Her superiors eventually ordered her to show Jobs, which she did comply, but stated that this decision to “give away the kitchen sink” to Jobs and his team, was their responsibility. As we know, Goldberg would be right, and the Macintosh desktop would revolutionize not only personal computers, but the way we read, listen to music, talk on the phone and now, watch television, all with the brand name of Apple, instead of Xerox. https://www.ithistory.org/honor-roll/dr-adele-goldberg
I sometimes cannot believe the age in which we live. We live in a time of history, that has seen the game of pong, lead to interactive global gaming. We live in a time that we can immediately find answers to almost any question. We live in time that keyboard interaction with digital devices is becoming voice activated. We have become pseudo doctors, plumbers, electricians, all by a click of a button. Human-computer symbiosis has been achieved. Thank you Smalltalk, thank you Goldberg and the team at PARC. May we all take advantage of their achievements, and safely connect through our digital device.